

Actual photo. Image Credit: Dio-V
That’s Not My House!
Chinese electronics company Xiaomi (pronounced: shao-mi) recently found itself in hot water over a recent ‘mix up’ which caused an undetermined number of users’ security camera feeds to be streamed to the wrong accounts. The first account of this behavior was reported by Reddit user “Dio-V” who wrote that by checking the camera feed on his Google Nest Hub device, he observed stills from office spaces, living rooms, and even children’s bedrooms. The issue appears limited to the Mijia brand of surveillance cameras, specifically the very affordable Mijia 1080P model which integrates with Google Assistant and Amazon Alexa.
In response, Google has disabled Xiaomi’s connection to Assistant, no changes to Alexa have been reported at this time. But just in case, it might be worthwhile to disconnect or disable these cameras until a fix is announced.
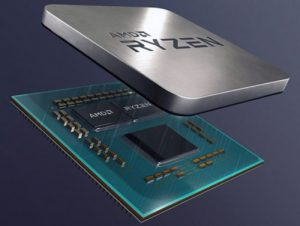
AMD “Ryzen” Above Intel
If you’ve noticed notebooks and PCs priced $100-$200 lower than usual, chances are they contain a chip from AMD known as Ryzen (rye-zen). For almost two decades, the ubiquitous “Intel Inside” or “i5”, or “i7” stickers could be found on nearly all OEM machines. But as of late 2019, some eagle-eyed shoppers noticed a different sticker in place of the aforementioned. In fact, we receive several calls every day regarding the reputation of this apparent newcomer “Ryzen”. We are happy to report the latest range of CPUs from AMD are the real deal.
Our Intel based editing machine from 2008 stickered for ~$5k, shod with a Xeon W3680 CPU. The processor had six processing cores (12 threads) and kept pace with modern variants for a decade. The Xeon was replaced with a Ryzen 3900X, which has 12 processing cores (24 threads) for less than $500, reliably doubling our output for far less money.
Competition is a good thing. It boosts innovation while driving down cost. In all cases the consumer wins. Intel has not successfully supplanted AMD’s recent success. Since Q3 of 2019, Intel brought several refreshes of existing hardware, coupled with price-cutting to preserve market share. These efforts have been in vain. Of course we don’t want AMD to become the Julius Caesar of PCs, so here’s hoping Intel can right the ship (and keep prices low) in 2020.


Blue Light Bad
Coffee is good, no wait, it’s bad, now it’s good, again… And now, blue light filters are bad? -Sorta.
A recent study released by Dr. Tim Brown of Manchester University suggests that earlier testing may not have accounted for the intensity of the light which reaches the eye. Put differently, previous studies inadvertently dimmed the amount of blue light reaching the eye when changing colors. This caused an uncorrelated effect on circadian rhythm. Dr. Brown’s study found that by carefully metering the intensity of the blue light to match that of white and yellow, the foremost had the least effect on the internal clock of mice used in the testing.
This is interesting stuff, though there’s no telling when a competing study will reverse the course once again.

